Privacy and encryption go together like peanut butter and jelly. At the very heart of most encryption strategies is a set of keys and a key exchange. Most of you have probably already heard of PGP (Pretty Good Privacy) and are confused about GPG. Generate a strong 4096 bit key gpg --full-generate-key List generated keys gpg --list-secret-keys Upload key to default servers gpg --send-keys <your_key_uid> Specify a specific remote server gpg --keyserver hkps://keyserver.ubuntu.com --send…
All posts in Linux
Installation: sudo pacman -S docker docker-compose Add yourself to the docker group: sudo gpasswd -a <USER> docker WARNING: Every user you add to the docker group is root equivalent. NOTE: It takes a reboot for this change to take effect. Enable and start deamon sudo systemctl enable --now docker.service docker.socket Common commands Build a container docker build -t <docker_name> . docker run -d -P <docker_name> OPTIONAL - Name your own docker instance name: sudo docker run -d --n…
Installing a package sudo pacman -S <package> Searching for a package sudo pacman -Ss <description/name> Removing packages To remove a single package, leaving all of its dependencies installed: sudo pacman -R <package> To remove a package and its dependencies which are not required by any other installed package: sudo pacman -Rs <package> Cleaning the package cache The built-in option to remove all the cached packages that are not currently installed is: sudo pacman -Sc To cl…
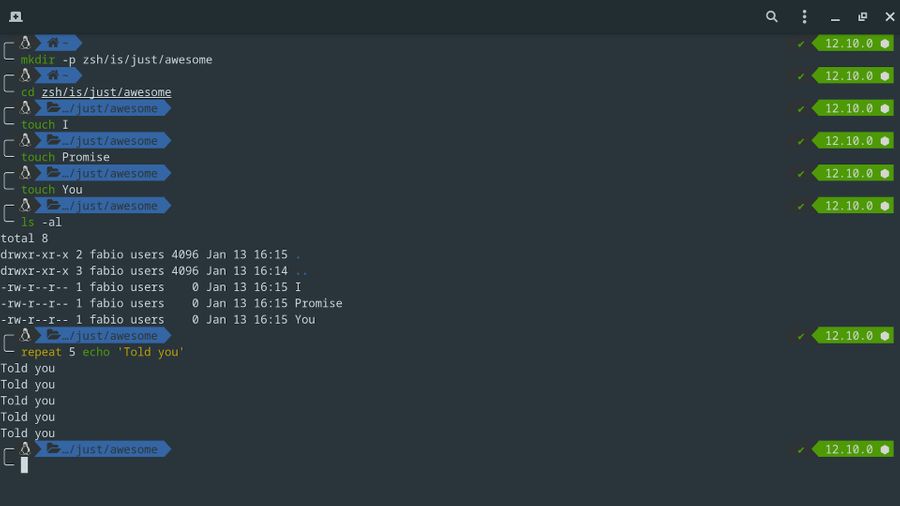
Most modern distributions still ship with Bash as the default shell. While there is absolutely nothing wrong with Bash in the slightest there is another popular kid on the block called ZSH. ZSH can do most if not all the things Bash can do but with a ton of extra features to boot. It is completely modular and can be installed and configured for low-end systems while also being able to be completely tricked out if performance is of no concern. Let's install and configure this amazing shell! sud…
If you've been wanting to try out Arch Linux on your machine but can't seem to figure out the right steps to install then this is the perfect post for you!